In today’s connected world, keyless access systems have become the norm. From office buildings to apartment complexes, RFID key fobs and RFID access cards have replaced traditional metal keys, offering a fast, convenient way to unlock doors with a tap. But with that convenience comes a question of practicality — what happens if you need a copy?
Whether you’re a property manager issuing duplicates, a business owner looking to streamline access for employees, or a tech-savvy user exploring how these systems work, understanding how RFID credentials can be cloned is essential.
What Is an RFID Key Fob or Access Card?
RFID stands for Radio Frequency Identification. A typical RFID access device — whether a key fob or a plastic card — contains a small microchip and antenna. When presented near an RFID reader, it wirelessly transmits a unique ID number to authenticate access.
There are various types of RFID credentials based on frequency:
- Low Frequency (125kHz): Common in legacy access control systems
- High Frequency (13.56MHz): Used in MIFARE cards and NFC-enabled devices
- UHF (860–960MHz): Typically for logistics and vehicle tracking
Copying such credentials requires understanding the frequency, chip type, and security mechanisms involved.
Is It Legal to Copy RFID Fobs?
The legality depends on intent and jurisdiction. In many cases, if you’re duplicating your own RFID access credential — with permission or for backup purposes — it’s legal. However, copying RFID credentials without authorization may violate property laws, rental agreements, or corporate security policies.
Always seek permission from your property management or access system administrator before cloning RFID fobs or cards.

How Does RFID Duplication Work?
RFID copying typically involves two main steps:
- Reading the data from the original key fob or card using an RFID handheld reader.
- Writing or emulating that data onto a blank RFID tag, card, or emulator.
Certain low-frequency tags (like EM4100, HID 125kHz) are easier to clone, while modern high-frequency or encrypted credentials (like MIFARE DESFire or HID iCLASS SE) include security keys that make copying extremely difficult — and in some cases, nearly impossible without professional tools.
Tools and Devices for Copying
There are open-source and commercial tools available that can read and duplicate basic RFID credentials:
- RFID handheld readers with read/write capabilities
- NFC-enabled Android phones (for some 13.56MHz cards)
- USB-based cloners for desktops and laptops
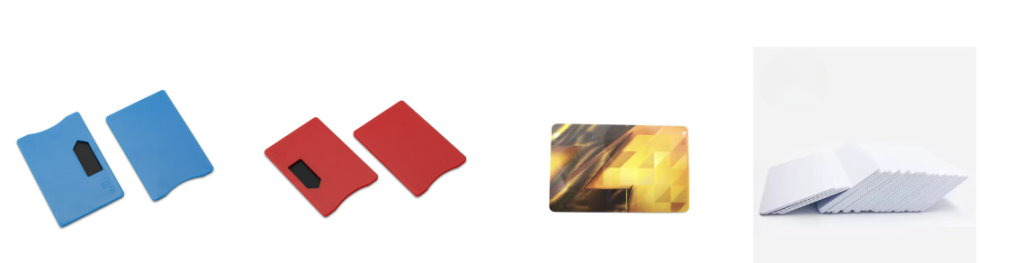
- Blank RFID cards, tags, or writable key fobs
Note: Many advanced access systems now use encryption, challenge-response protocols, and mutual authentication. These protections help prevent unauthorized cloning — and highlight why relying on secure chips is critical for enterprises.
Use Cases: When Copying Makes Sense
- A landlord needs to issue another RFID fob for a new tenant
- A factory wants to test and deploy duplicate employee badges
- A homeowner wants a backup card in case of loss
- System integrators testing compatibility with various RFID chips
In all of these scenarios, understanding the type of RFID credential and the right hardware to read and write them is crucial.
Learn More: In-Depth Guide on RFID Cloning
Want to explore the tools, chipsets, and methods used in real-world RFID copying and testing?
Read the full guide here
This detailed breakdown from JIA RFID Technology Co., Ltd. covers chip types, compatible readers, ethical considerations, and best practices for RFID access duplication and secure system design.
Other articles from totimes.ca – otttimes.ca – mtltimes.ca




















